Today’s cybersecurity landscape is changing in waves with threat and attack methods putting the business world on high alert. Modern attacks continue to gain sophistication, staying one step ahead of traditional cyber defense measures, by continuously altering attack techniques. With the increasing use of AI, ML, 5G, and IoT, network speeds readily run at 100G rates or more. Current methods of detection for dangerous threats and attacks are quickly becoming outdated and ineffective.
When operating at modern network speeds, it is no longer possible for security teams to monitor an entire network in real time. Organizations have tried to augment their Intrusion Prevention Systems (IPS) by relying on employees to perform the deep analysis of suspicious activity. This requires highly trained and paid security operations center personnel and comes with significant risks when teams are unable to keep pace with the deluge of data.
The litany of security issues has forced organizations to seek a next-generation solution that provides the ability to analyze all traffic within their 100G networks. To accomplish this requires a next generation IPS that is automated, more effective, and efficient that can stop attacks in real time at 100G and beyond.
ARIA Zero Trust Security Gateway on BlueField-2 Data Processing Unit
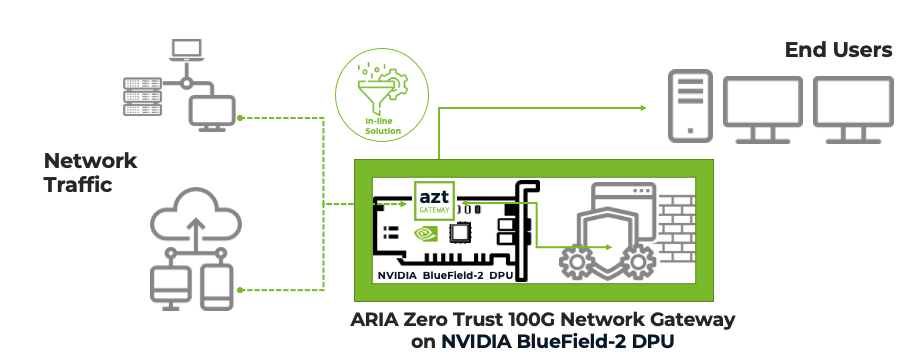
ARIA Cybersecurity has developed a solution to solve these problems called the ARIA Zero Trust (AZT) Gateway. The gateway uses hardware acceleration from the NVIDIA BlueField-2 Data Processing Unit (DPU) for line-rate analysis. The solution is deployed as a compact, in-line, standalone network device to stop attacks with no impact to production traffic crossing the wire.
To accomplish this, the gateway operates by analyzing each packet in real time. Creating analytics for threat analysis enforces not only existing standalone protection policies, but also new dynamically generated policies, to ensure a more effective security posture.
To detect attacks, the packet analytics go to the central brain of the solution. The brain is ARIA’s Advanced Detection & Response product that uses ML and AI-driven threat models to analyze data for over 70 different types of attacks using the MITRE ATT&CK framework.
This is accomplished in a totally automated approach, removing the need for manual human involvement. In addition, copies of specific traffic conversations can be sent to an Intrusion Detection System for deeper analysis.
In both cases, the results are relayed back to the AZT Gateway as dynamically generated rules to eliminate the identified attack conversations in real time. Attacks can be identified, logged as new rules, and stopped in just seconds, automatically. Performing this process in real time is a major breakthrough.
Previously, you may have only been alerted to a problem and left to figure out the solution on your own. However, with the AZT Gateway, you can now take automated action on alerts and deploy new security rules to prevent unwanted activities on your network.
Real-time security analysis
The BlueField-2 DPU is available in a compact PCIe OCP Card form factor. It provides the ability to monitor two 100G links at a time, without dropping any traffic or consuming critical CPU resources.
BlueField also provides hardware acceleration to handle packet analysis at demanding networking speeds in excess of 100G. To classify each packet at a conversation level, the AZT system software leverages the highly efficient BlueField Arm cores to apply preset and dynamically generated security rulesets.
The compact footprint and low-power draw make BlueField ideal for deployment in network provider and Cloud data center environments. Using BlueField, the AZT Gateway can also look into encrypted data stream payloads for deeper analysis.
This solution has proven to lower the cost per protected packet by up to 10X, decrease power compared to alternatives, and reduce the rack footprint by 10X.
For upcoming enhancements, the NVIDIA Morpheus application framework will provide ARIA with evolving cybersecurity analysis using advanced ML and AI algorithms to find and stop sophisticated attacks in real time.
Watch the ARIA Zero Trust Security Gateway webinar. >>
Learn how to accelerate your network with the BlueField DPU. >>
